- Ssh Shell 16 09 – Secure One Click Log Inbox
- Ssh Shell 16 09 – Secure One Click Log In Excel
- Ssh Shell 16 09 – Secure One Click Log In Php
- Ssh Shell 16 09 – Secure One Click Log In Stock
Ssh Shell 16 09 – Secure One Click Log Inbox
If you uploaded SSH keys to your account and chose Add SSH Keys upon Droplet creation, you can connect to the Droplet using your preferred SSH client or command line. If you did not use the SSH option, the Droplet's password is the password you set during creation. Here's the entry from the 'secure' log: Apr 23 08:17:09 serv unixchkpwd18023: password check failed for user (xxxcPanelUsernamexxx) Apr 23 08:17:09 serv sshd18020: pamunix(sshd:auth): authentication failure; logname= uid=0 euid=0 tty=ssh ruser= rhost=37.78.111.37 user=xxxcPanelUsernamexxx. Macbooster 3 1 5 – maintains and optimizes your system. Gnome-terminal -x ssh -X email protected b. Under Mac: sftp://email protected terminal -x ssh email protected c. Under Windows: use WinSCP -for help with setting up winSCP, see post #4 or putty (thanks boardsportsrule) Shortcuts make things easier to access. Creating shortcuts will allow you one-click wireless dual mount, or one-click. REST services on the JD Edwards EnterpriseOne AIS Server can use HTTP Basic Authentication for access. Support for HTTP Basic Authentication is enabled out of the box and is required to run the EnterpriseOne Orchestrator Client, create custom Java calls from orchestrations, and use the AIS client Java API (versions 1.2.1.x and higher). Setting /sbin/nologin as the user's shell (or /bin/false or /bin/true, which are almost equivalent) forbids the user from logging in to run any command whatsoever.SSH always invokes the user's login shell to run commands, so you need to set the login shell to one that is able to run some commands.
Ssh Shell 16 09 – Secure One Click Log In Excel
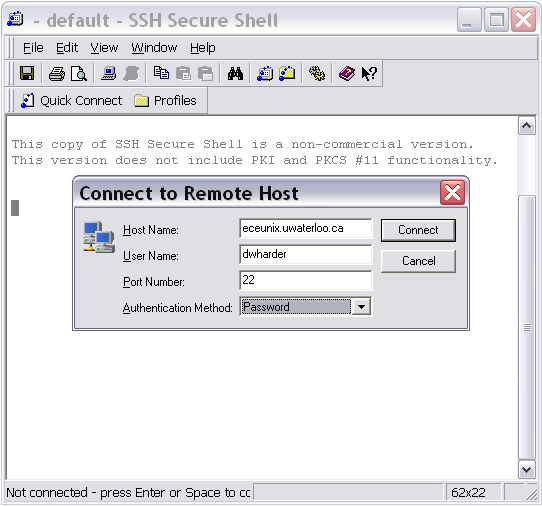
When you connect to a host for the first time, SSH Secure Shell for Windows asks if you want to accept the server's encryption key. If you choose to accept and save it, SSH Secure Shell stores the key in its list of host keys. Livequartz 2 0 2. If SSH Secure Shell ever receives a key from this host that doesn't match the saved key, it will alert you that the host's key has changed.

When you connect to a host for the first time, SSH Secure Shell for Windows asks if you want to accept the server's encryption key. If you choose to accept and save it, SSH Secure Shell stores the key in its list of host keys. Livequartz 2 0 2. If SSH Secure Shell ever receives a key from this host that doesn't match the saved key, it will alert you that the host's key has changed.
Ssh Shell 16 09 – Secure One Click Log In Php
One of the possible reasons for this change is a man-in-the-middle attack, which means that a malicious computer is posing as the host you are trying to reach in order to capture data passing between your computer and the host computer. Another more benign reason may be that the host has updated its SSH software, in which case you will have to receive a new host key. Tipard blu ray converter for mac 9 2 18 x.
Ssh Shell 16 09 – Secure One Click Log In Stock
Before downloading a new key, you should first verify with a trusted source (for example, the host's system administrator) that the legitimate host has had its SSH software upgraded or changed. Then, to delete the old host key and accept the new key:
- From the Edit menu, select Settings...
- If it is not already expanded, double-click GlobalSettings to expand it.
- If it is not already expanded, double-click ServerAuthentication, and under it, click Host Keys.
- Select the name of the host for which the key has changed, and then click Delete.
- The next time you connect to the host, a dialog box titled
Host Identificationwill appear, asking if you want to accept the new host key. Click Yes to accept and save the new key.
